How Does Cyber Insurance Shape Incident Response?
This blog post originally appeared on cyber-economics.com, a new venture by a friend and colleague. Essentially, I summarise our WEIS’21 paper.
=======
We discovered set of perspectives arguing that insurers have created a cybersecurity equivalent of the unified fire brigade set up by insurance companies in 1833 to protect (mostly insured) properties in London and was only taken over as a public service and expense in 1865. In the context of cyber insurance, the industry did so by creating hotlines for insureds to call upon discovering an attack. The hotline operator then assembles a team of responders spanning forensic investigation, legal advice, and public relations who rapidly contain the attack and restore the firm’s business operations. These teams are especially efficient because insurers send work to a small number of firms who build up trust and knowledge of each other’s processes. We call this perspective the democratization of incident response.
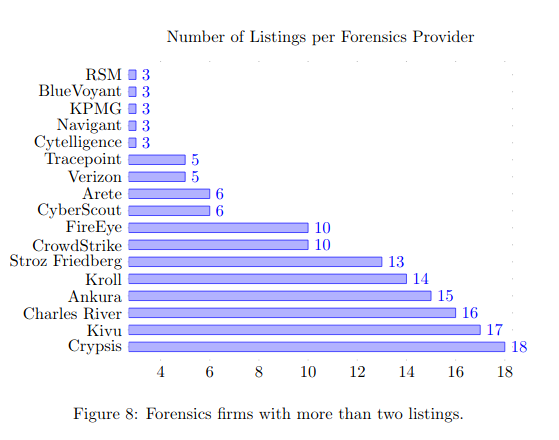
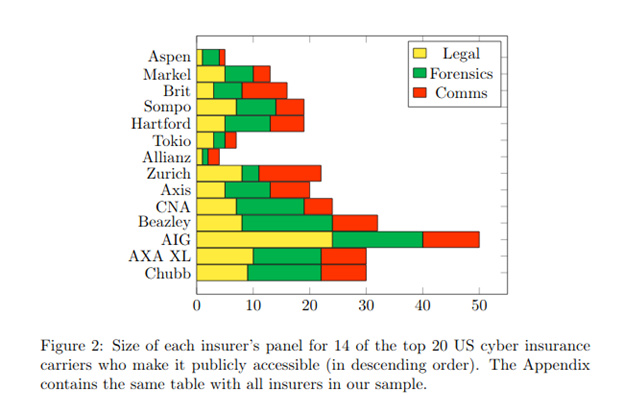
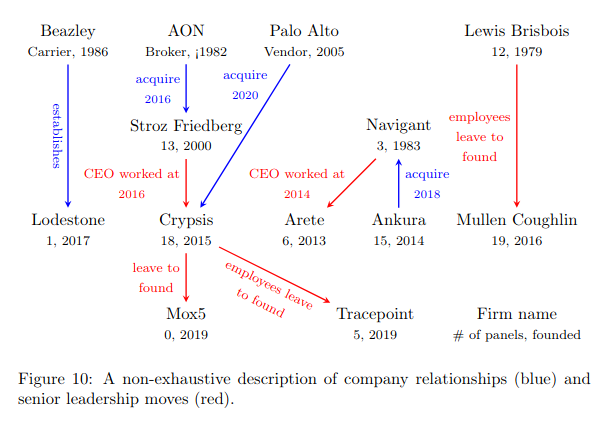
A dissenting view focuses on how insurers funnel work to its panel of incident response firms, generally less than ten firms. Our research discovered the same few IR firms re-appear on insurers’ panels. So why do those IR firms get so much work? Such firms are added to panels because they agree to provide services at a low hourly rate, even fixed prices for some investigations, and have built a relationship with insurers by employing various strategies.
Some IR practitioners argue that these prices are unsustainable and drive quality out of the market. Indeed, it is true that many insider IR firms are operating with venture capital funding. They also tend to be service based firms who have no pre-existing access to the victim’s network, which makes data capture and preservation tricky. Such concerns can be summarised by the term “the commoditisation of incident response.”
Did insurers both increase access to incident response while simultaneously have reducing the average quality of investigation? Did insurers democratise or commoditise incident response? How can we reconcile the two perspectives? Like a typical academic, I argue both can be true providing insurers triage effectively.
Governments set up emergency hotlines in order to effectively distribute emergency resources. The operator sends one fire brigade with low urgency to rescue a cat from a tree, but sends a fleet of fire brigades including reservists upon a report of a power plant fire. Insurers are providing the same function when it comes to cyber incidents.
If a small business calls the hotline about a business email compromise, then a low-cost remote investigator is engaged at a fixed price. If a MSSP vendor is compromised leading to the potential of ransomware infections at hundreds of firms, then a more sophisticated incident response is required. This seems like common sense but it is not clear who was coordinating this before cyber insurance came along. In fact, it seems like small businesses were left somewhat stranded. Mainstream IR firms commonly served companies with large security budgets, often by offering integrated monitoring and response solutions. Such firms specialised in responding to sophisticated attacks and could draw on the sophisticated data processing capabilities provided by having products installed in the victim’s environment. It is a fair comment that service-based firms working for cyber insurers cannot easily match this level of response. But it is also true that small businesses cannot afford this level of response.
Thus, our study finds that cyber insurance has shaped incident response in two main ways: (1) establishing incident hotlines that coordinate response resources by triaging cyber incidents; (2) making possible an IR business model that can serve firms with low IT maturity and that does not rely on pre-existing network access. This story should be celebrated and is indeed similar to insurers’ creating a unified London fire brigade in the 1800s.
Nevertheless, attention must be paid to how insurers operate this triage function. First, the internal processes by which insurers add IR firms to panels are often opaque and this prevents open competition for IR work leading a small number of firms to get the majority of work. Secondly, hotlines are often operated by law firms who have their own incentives when it comes to incident response, likely prioritising mitigating litigation risk over technical risk. Thirdly, calling a hotline is likely sub-optimal compared to following an ex-ante plan, not least because data collection and preservation cannot be established after the incident has already occurred.